Table of Contents
How To Mitigate The New Remote Code Execution Vulnerability In Dompdf
Maximilian Kirchmeier and and Fabian Bräunlein security researchers from Positive Security have revealed a new remote code execution vulnerability in dompdf. It’s a PHP-based HTML to PDF converter that could execute remote code if exploited successfully. This vulnerability has significant outcomes on websites requiring the server-side generation of PDFs. It depends on user-supplied data (such as ticket purchases and other receipts), especially when inputs are not sanitized adequately to mitigate the XSS vulnerability or when the library is installed in publicly-accessible directories. This post will discuss how to mitigate the new remote code execution vulnerability in dompdf.
What Is Dompdf?
Dompdf is an HTML to PDF converter. It’s a CSS 2.1 compliant HTML layout and a rendering engine written in PHP. dompdf is a style-driven renderer that downloads and reads external stylesheets style attributes of individual HTML components and inline style tags. Moreover, it supports many presentational HTML attributes.
Key Features
Handles CSS 2.1 and a few CSS3 properties, such as @media, @import, and @page rules.
Supports external stylesheets
Supports presentational HTML 4.0 attributes
Supports complex tables, such as row and column spans, individual cell styling, and separate and collapsed border models
Inline PHP support
Image support
Basic SVG support
Summary Of The New Remote Code Execution Vulnerability In Dompdf:
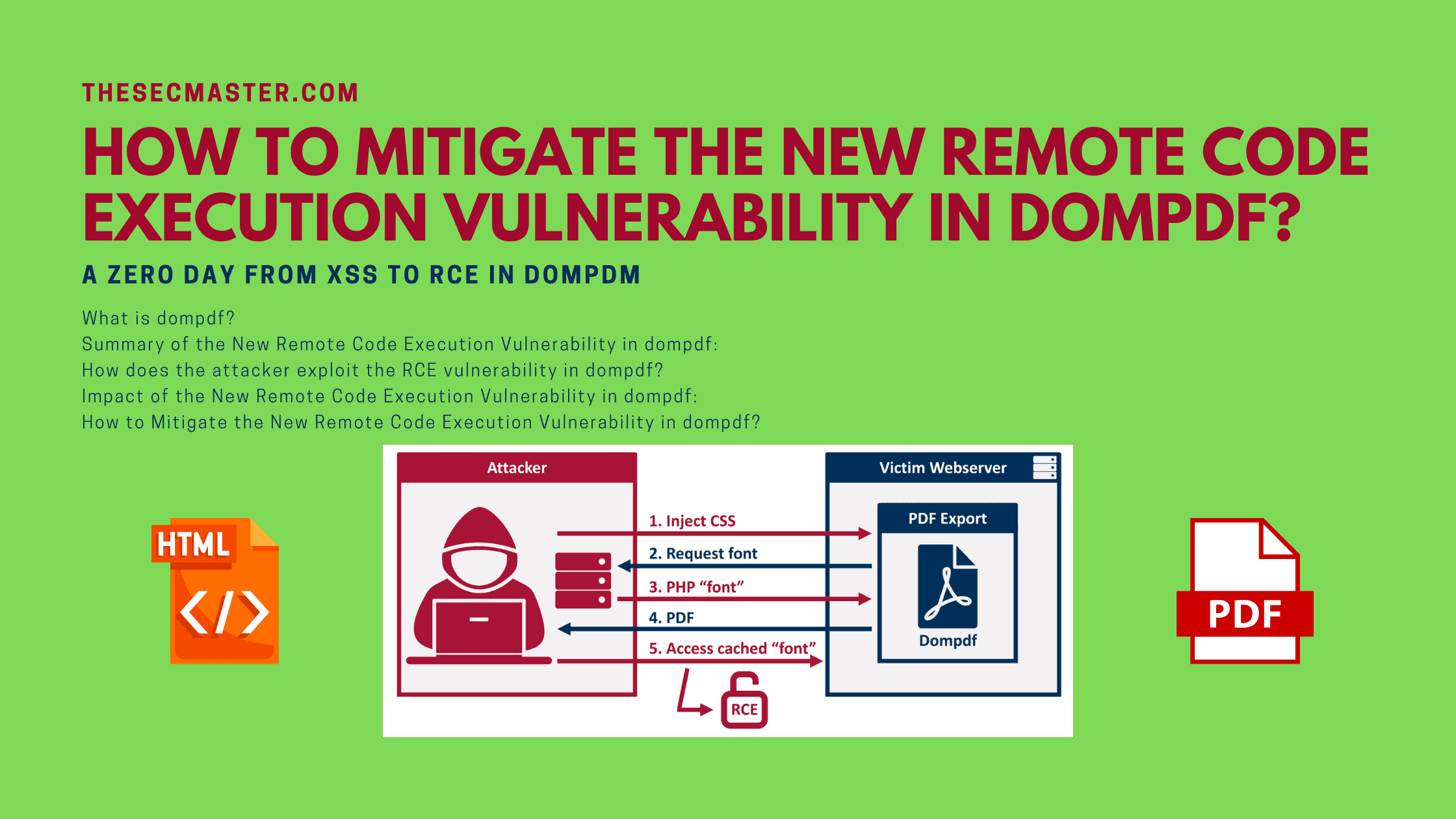
The famous PHP library dompdf suffers from a vulnerability allowing Remote Code Execution in specific configurations. Inject CSS into the data processed by the dompdf. It can be tricked into storing a malicious font with a .php extension in the font cache, which can be executed by accessing it from the web later. The vulnerability allows malicious actors to upload the font file with a .php extension to the web server, which can be activated through an XSS vulnerability to inject HTML into a web page before rendering it a PDF.
How does The attacker Exploit The RCE Vulnerability In Dompdf?
Created by Positive Security
A malicious user can use dompdf for remote code execution under the following scenarios.
the dompdf font directory is accessible through the web
a remote user can inject CSS into the document rendered by dompdf
On a vulnerable system, a user can reference a specifically crafted font file that can pass the initial parsing process. It can be processed when the dompdf persists the font file to the font directory with an extension that matches the file on the remote system. At this point, the user can load the persisted file to execute code within the context of the PHP process.
When $isRemoteEnabled is set, dompdf lets you load custom fonts using font-face CSS rules. Dompdf caches it locally in the /lib/fonts sub-directory when the external font is used and adds a corresponding entry in the dompdf_font_family_cache.php through saveFontFamilies().
Impact Of The New Remote Code Execution Vulnerability In Dompdf:
Various use cases require the server-side generation of PDFs that contain user-supplied input. These include ticket purchasing, invoices/receipts, and other automated email service providers. It is possible that some of these services can be affected if the following preconditions are fulfilled.
dompdf is installed in the directory accessible through the web.
PDFs are being generated through insufficiently sanitized input. It can be caused through an XSS or by directly passing user data to the backend.
dompdf version below or 0.8.5 is used or $isRemoteEnable is set to true.
How To Mitigate The New Remote Code Execution Vulnerability In Dompdf?
Here are steps you can take to mitigate the new remote code execution vulnerability in dompdf.
Ensure that dompdf is not installed in the web-accessible directory.
Move dompdf and the dompdf font directory outside the web root.
Double-check the input sanitization performed before passing data to dompdf. It prevents hackers from injecting HTML/CSS.
Update dompdf to a latest version and turn off $isRemoteEnables.
Keep an eye out for the dompdf patches that fix the vulnerability and apply it when available.
How to Upgrade dompdf to the Newest Version?
You can upgrade dompdf to the latest version using the following steps.
Use Composer for easy dependency management.
If you do not use Composer, you can download the packaged release of dompdf that includes all files required to use the library.
Click the link labeled ‘dompds_0.8.6.zip’ for package release.
The two buttons labeled ‘Source Code’ are auto-generated and do not include all dependencies.
We hope this post would help you know How to Mitigate the New Remote Code Execution Vulnerability in dompdf. Please share this post and help to secure the digital world. Visit our social media page on Facebook, LinkedIn, Twitter, Telegram, Tumblr, & Medium and subscribe to receive updates like this.
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.