Table of Contents
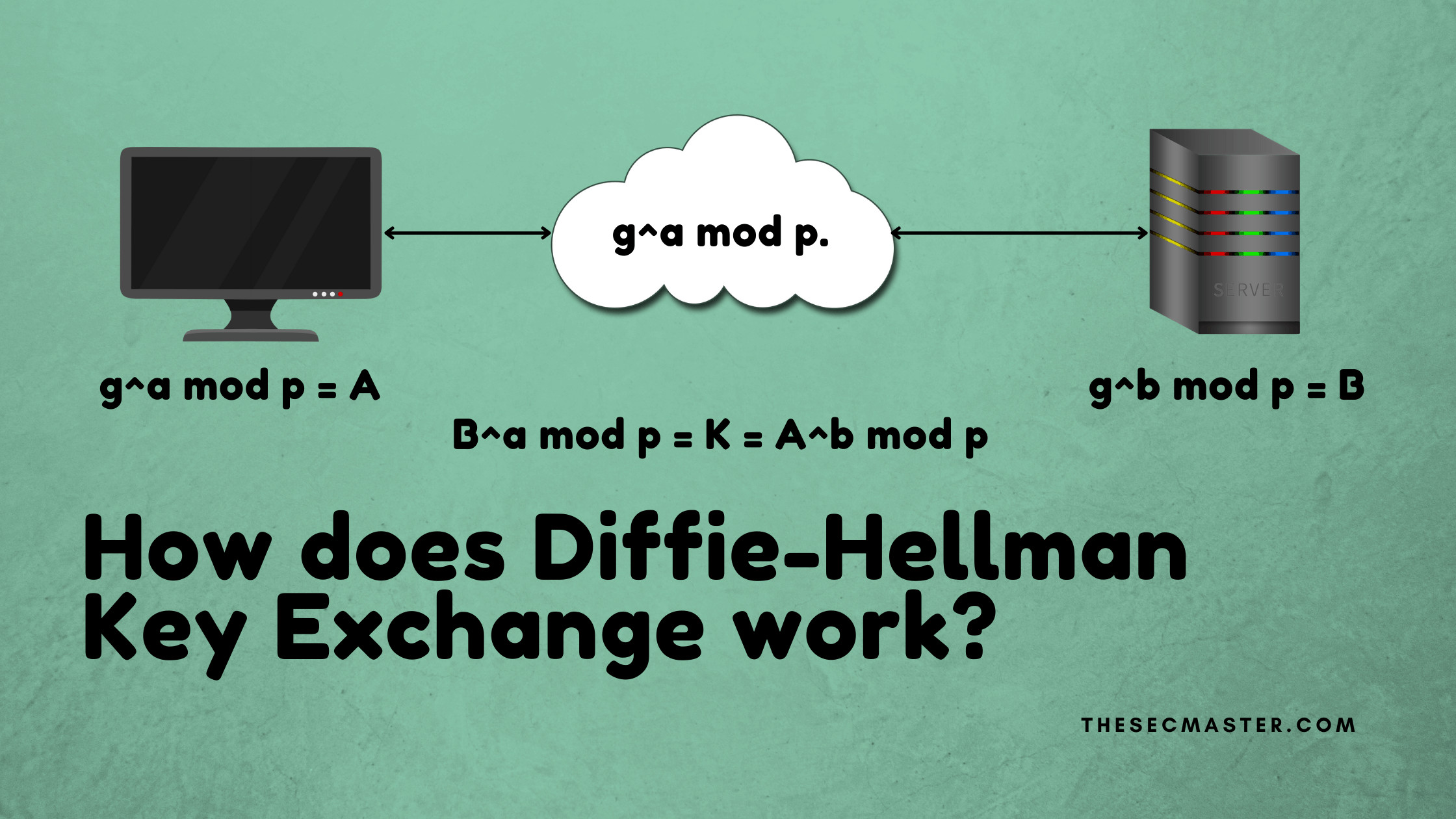
A Mathematical Explanation of the Diffie-Hellman Key Exchange Protocol:
Whitfield Diffie and Martin Hellman created a cryptographic key exchange protocol in 1976 called Diffie-Hellman Key Exchange. This protocol offers a safe way to exchange the secret key even if an intruder intercepts the traffic. In feature made it so popular that DH key exchange started becoming part of the most asymmetric encryption algorithms. Because of its popularity, it is worth understanding the logic behind the Mathematical explanation of the Diffie-Hellman Key Exchange protocol
Symmetric Encryption:
This encryption system uses the same key to encrypt and decrypt the data. This is easy and simple to implement. However, the main concern comes in the matter of trust. How to trust the other side of the entity is legitimate. There is a high risk of sharing a decryption key with an unknown entity. On the public network like the internet, never. If the key gets leaked, any buddy can decrypt the data on the internet. To overcome this problem second method of encryption that is asymmetric encryption, is introduced.
Asymmetric Encryption:
Actual encryption happens in asymmetric encryption protocols. Asymmetric encryption is introduced to overcome the problems of symmetric encryption. This encryption system uses two keys: public and private, instead of one key. People often say that a private key is used for encryption and a public key is used for decryption. It is partially true, in my opinion. Both public and private keys will take part in the encryption and decryption process. After the completion of a key exchange process between the two parties, both parties create a new key that will work as a symmetric key. In asymmetric encryption, there will not be a physical key exchange, but logically yes. This gives a big lead to this system over symmetric encryption.
Explanation Diffie-Hellman Key Exchange Protocol
Let’s see how key exchange happens in the simple calculation: let’s assume ‘a’ is a private key of the client. And ‘b’ is a private key of the server. Two prime numbers, ‘p’ and ‘g’ are public keys that will be shared with both client and server.
p = 149
g = 17
a = 6
b = 8
The mathematical formula to create an encrypted key is g^a mod p.
The mathematical formula to create an encrypted key is g^a mod p.
Phase #1:
Step 1: When the Client requests a connection to the server. The server sends a public certificate with ‘p’ and ‘g’ values.
The server sends a public certificate with ‘p’ and ‘g’ values
Step 2: Client generates Client encryption key. client encryption key = 17⁶ mod 149 = 16
Step 3: The server generates its encryption key. server encryption key = 17⁸ mod 149 = 5
Generating Client and Server encryption keys
Step 4: Both Client and Server exchange their encryption keys.
Client and Server exchanging their encryption keys.
At the end of phase 1, if someone is listening to the traffic, he would be able to capture four numbers. p, g, client encryption key, and server encryption key. What he doesn’t know is a and b.
Phase #2:
Step 5: Both Server and Client use the same mathematical function to calculate the key.
Client key: (server encryption key)^a mod p = 5⁶ mod 149 = 129
Server key: (client encryption key)^a mod p = 16⁸ mod 149 = 129
Both Server and Client use the same mathematical function to calculate the key.
In this example, 129 is the key that works as a symmetric key.
At the end of phase 1, if someone is listening to the traffic, he would be able to capture four numbers. p, g, client encryption key, and server encryption key. What he doesn’t know is a and b.
This completes the key exchange process. As we said earlier, there will not be a direct key exchange between the two parties, but the result of phase 2 serves as a symmetric key.
Thanks for reading this article. Please visit our site to read such interesting articles.
You may also like these articles:
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.