Table of Contents
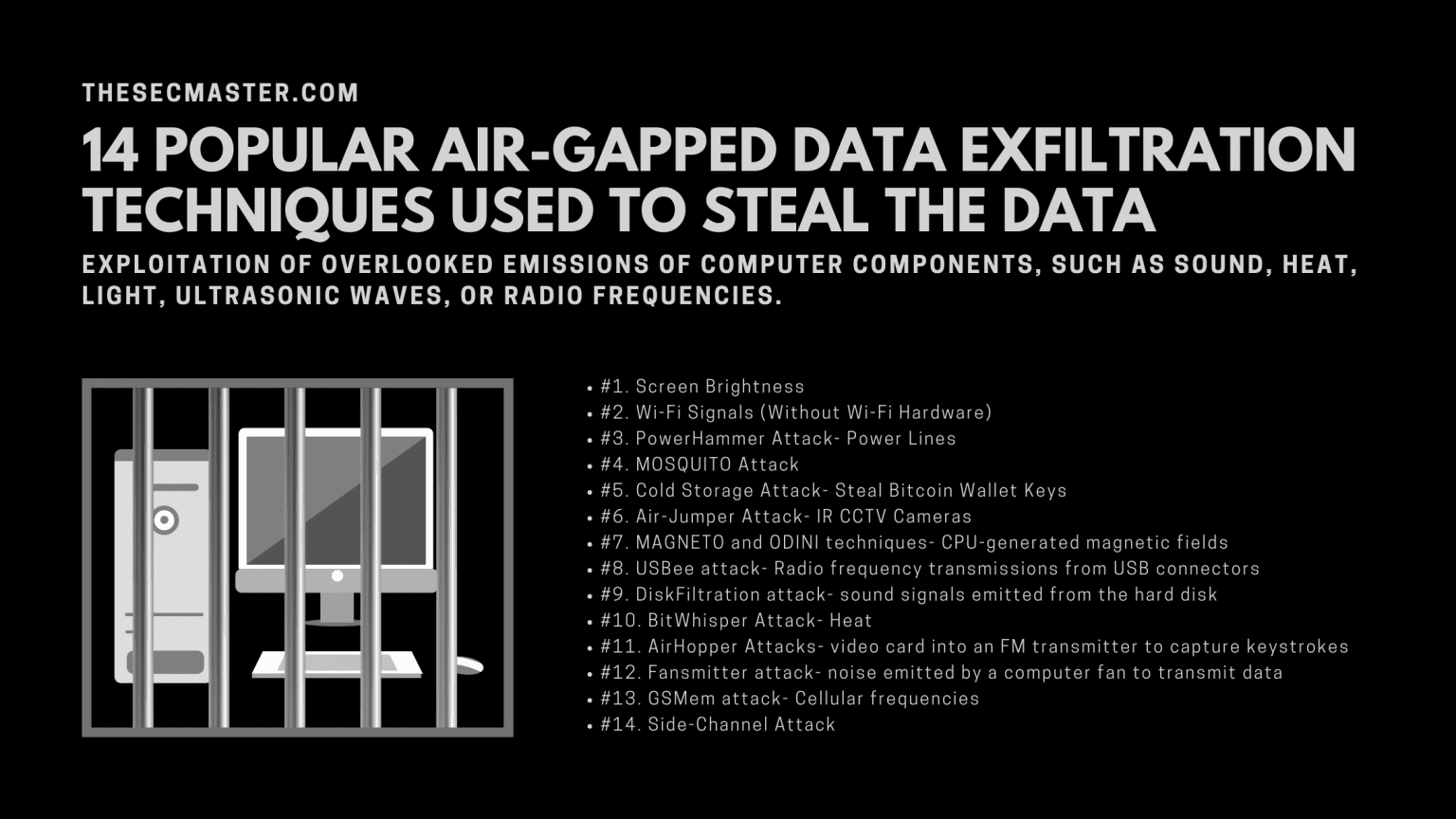
14 Popular Air-Gapped Data Exfiltration Techniques Used to Steal the Data
Advanced technologies come with a lot of potential threats. The more we are connected to the Internet, the more we are in trouble. Cybercriminals are always in search of loopholes to infiltrate the system. It may sound weird or unreal, but criminals can exfiltrate data from your system by simply changing the screen brightness.
In recent years, various cybersecurity researchers have demonstrated innovative methods to exfiltrate data from a physically isolated air-gapped system that can not connect physically or wirelessly with other systems or network devices. These ideas rely on exploiting overlooked emissions of computer components, such as sound, heat, light, ultrasonic waves, or radio frequencies.
These unusual techniques, which may sound useless or theoretical, could play a vital role in exfiltrating data from an infected but air-gapped system. In this article, we will discuss the most common air-gapped data exfiltration techniques. Let’s get started with an introduction.
What Is Air Gapping?
An air gap is a security measure in which computers, networks, and other systems are not connected to other computers, networks, or devices. It is used in instances that need air-tight security without the risk of a disaster or compromise. Air gapping ensures the complete isolation of a given system electronically, electromagnetically, and physically.
In simple words, data can be transferred by only connecting a physical device to it, such as an external hard disk, flash drive, or DVD. Air-gapped protect computers and networks from keyloggers, ransomware, malware, or other unwanted access. Common examples include financial computer systems, government networks, or computerized medical equipment.
What Are The Benefits of Air Gapping?
Here are some of the benefits of air gapping.
The data can’t be updated to reflect the ongoing changes, so the risk becomes stale.
It’s a fantastic way to safeguard your critical infrastructure.
It provides greater security than conventional backup architecture.
Air gapping techniques limit the ability of malware to spread.
It creates more work for criminals to get air-gapped data.
It improves the odds of recovering from attacks.
The air gap might prevent data leakage or destruction due to power fluctuations.
The computer or network is protected from any malware circulating the Internet.
It is considered the most reliable way of securing information and data from hackers due to a lack of connection.
14 Popular Air-Gapped Data Exfiltration Techniques
Despite the high level of security created by an air gap, some modern techniques have been anticipated to find a way to breach air-gapped systems. Here are some of the most popular air-gapped data exfiltration techniques.
#1. Screen Brightness
Attackers can steal data from air-gapped systems without requiring physical contraction or network connectivity with devices. Malware on a compromised system can get sensitive data, such as images, files, passwords, and encryption keys, modulating it with the screen brightness. In this technique, criminals use slight modifications in the LCD screen brightness that remain invisible to the naked eye.
Cyber Security Labs @ Ben Gurion University
It is done to modulate binary information in morse-code-like patterns. On the other hand, hackers can collect this data stream via a video recording of the compromised system’s display. It can be taken by a smartphone camera, local surveillance camera, or webcam and then reconstructed exfiltrated information through image processing techniques.
#2. Wi-Fi Signals (Without Wi-Fi Hardware)
Sensitive data could be exfiltrated through air-gapped systems using a technique that uses Wi-Fi signals as a covert channel without requiring the presence of Wi-Fi hardware on targeted systems. Air-gapped systems with no network interfaces are considered a necessity in environments where critical data is involved in reducing the risk of data leakage.
Cyber Security Labs @ Ben Gurion University
The transmitting and receiving systems must be located close to each other to attack such systems. The AIR-FI is unique in the way that method neither relies on a Wi-Fi transmitter for generating signals nor needs kernel drivers, or special privileges such as access to hardware resources for data transmission. The covert channel can work from within an isolated virtual machine, having an endless list of Wi-Fi-enabled devices that can be compromised by an attacker.
#3. PowerHammer Attack- Power Lines
Dubbed PowerHammer is the latest technique that controls CPU utilization of an air-gapped system through specially designed malware and causes fluctuations in the current flow in the morse-code-like patterns for transferring data hints in binary forms.
To retrieve modulated binary information, the hackers need to implant hardware to monitor the current flow and then decode the exfiltrated data. Attackers can exfiltrate data from a system at a speed of 10 to 1000 bits per second based on their approach.
#4. MOSQUITO Attack
MOSQUITO is a new technique that works by reversing connected speakers into the microphone by exploiting a specific audio chip feature. Since some headphones/speakers/earphones respond well to a near-ultrasonic range, such hardware can be reversed to work as a microphone.
Cyber Security Labs @ Ben Gurion University
When it comes to secret communication, it’s evident that two computers can not exchange data through audible sounds, such as headphones and speakers. Therefore, inaudible ultrasonic waves provide the best acoustic covert channel for speaker-to-speaker communication.
#5. Cold Storage Attack- Steal Bitcoin Wallet Keys
Cold storage attacks are not a new hacking technique. In this technique, all previously discovered out-of-band communication methods can be leveraged to steal private keys for a crypto wallet installed on cold storage, preferably a Raspberry Pi or air-gapped computer.
Cyber Security Labs @ Ben Gurion University
Keeping the cryptocurrency protected in a wallet on an offline device is called cold storage. In the adversarial attack model, a hacker infiltrates the offline wallet and compromises it with malicious code. The malware can be pre-installed or pushed in during the initial wallet installation. It can also infect the system when portable media is inserted into the wallet to sign a transaction.
Cyber Security Labs @ Ben Gurion University
#6. Air-Jumper Attack- IR CCTV Cameras
Another technique to steal sensitive information from the air-gapped system is with the help of infrared-equipped CCTV cameras used for night vision. A new attack scenario, dubbed aIR-Jumper, includes a compromised air-gapped system and an infected CCTV network, assuming that both are isolated and none of them is internet-connected.
To read and transmit data, the aIR-Jumper malware installed on the air-gapped system and CCTV network blink IR LEDs in the morse-code-like patterns for sending files into the binary data. However, the attack is used to steal files in binary data, so hackers can not steal any large files. But they could get their hands on cryptographic keys, passwords, PIN codes, and other sensitive data.
#7. MAGNETO and ODINI techniques- CPU-generated magnetic fields
Dubbed MAGENTO and ODINI techniques make use of proof-of-concept malware installed on an air-gapped system inside the Faraday cage for controlling the magnetic fields emanating from the system by regulating the workload on the CPU cores.
Cyber Security Labs @ Ben Gurion University
Cyber Security Labs @ Ben Gurion University
Once an attacker succeeds in planting malware on an air-gapped system, the malware then gathers small pieces of information, such as encryption keys, keylogging data, passwords, and credential tokens. The PoC malware then electrically generates a pattern of magnetic field frequencies by regulating the workload.
#8. USBee attack- Radio frequency transmissions from USB connectors
Dubbed USBee technique comes with a significant improvement over the NSA-made USB exfiltration called CottonMouth. Unlike CottonMouth, USBee does not need an attacker to smuggle an altered USB device into the targeted air-gapped computer. Instead, it turns USB devices inside the facility into an RF transmitters with no changes.
Cyber Security Labs @ Ben Gurion University
USBee turns the targeted system’s USB ports into mini Radio Frequency transmitters by modulating the data inserted into plugged-in devices at high speed. It will then transmit a string of ‘0’ bits to a USB port, and the device generates detectable emissions between 240MHz and 480 MHz frequencies.
#9. DiskFiltration attack- sound signals emitted from the hard disk
This technique is used to steal sensitive data from an infected system, even if it has not been connected to the Internet, to prevent the computer from leaking information stored in it. You might have observed something spinning and making weird noises while your system reads or writes data on a storage hard drive.
Cyber Security Labs @ Ben Gurion University
It’s called an actuator, the voice coil, inside the hard drive that moves on the disk plate while accessing certain storage blocks. This technique is fast enough to transmit a 4096-bit key within 25 minutes via manipulated sound signals emitted from the hard disk drive.
#10. BitWhisper Attack- Heat
This new technique enables attackers to steal passwords or security keys from a secured computer and send sensitive data to an internet-connected device placed in close proximity controlled by them. They could also use their internet-connected devices to send malicious commands to the air-gapped system via the same heat and sensor methods to cause more damage to the secured infrastructure.
Cyber Security Labs @ Ben Gurion University
Thermal sensors present in systems trigger internal fans to cool down the system if overheating components such as GPU, CPU, and other motherboard elements threaten to damage them. BitWhisper leverages these sensors to send commands to air-gapped computers and extract data from them.
#11. AirHopper Attacks- video card into an FM transmitter to capture keystrokes
AirHopper is a keylogger application to track what is being typed on the system or mobile phone. It’s a special kind of keylogger because it uses frequencies to send data from a system, all by exploiting the computer’s monitor to evade air-gap security measures.
Cyber Security Labs @ Ben Gurion University
The technology works by leveraging the FM radio receiver included in some mobile phones. AirHopper can capture keystrokes by intercepting specific radio emissions from the display unit or monitor of an isolated system.
#12. Fansmitter attack- noise emitted by a computer fan to transmit data
Fansmitter is malware that can acoustically exfiltrate data from the air-gapped system, even when speakers and audio hardware are not present. This technique leverages noise emitted from the CPU and chassis fans present in every computer virtually. The software can regulate the internal fans’ speed to control the acoustic waveform emitted from a system.
Binary data can be modulated and transmitted over the audio signals to a remote microphone. Fansmitter designs include acoustic signature analysis, data transmission, and data modulation. Using this technique, data from an air-gapped system can be transmitted without audio hardware.
#13. GSMem attack- Cellular frequencies
Despite all these sophisticated techniques of equipment to hack an air-gapped system, you can do it using a cell phone, even an old-fashioned or dumb phone. Hacking an air-gapped system can be done using a basic low-end phone.
Cyber Security Labs @ Ben Gurion University
This hack attack that can steal data from a highly secured system uses electromagnetic waves, the GSM network, and low-end mobile phones. The attack relies on malware installed on both the mobile phone and the air-gapped system. It allows hackers to steal sensitive information, such as encryption keys, passwords, or even GPS coordinates, from a highly secured air-gapped system.
#14. Side-Channel Attack
Side-Channel attack extracts the secret cryptographic key from a computer by analyzing the pattern of electromagnetic outputs and memory utilization of the PC emitted during the decryption process.
These attacks conducted against electronic infrastructure and equipment are relatively inexpensive and simpler to execute. Criminals do not need to know specific implementation details of the cryptographic device to execute these attacks and extract keys.
Final Words
The best practice is to be realistic about air gapping. It can work and can be very effective in the right circumstances. You should not adopt a simplistic mindset and think the system is air-gapped, so it’s secure. This concept no longer works.
However, it’s important to think about the desired outcomes, vulnerabilities, and risks for a particular air gap technique. In this article, we have discussed the most popular air-gapped data exfiltration techniques. Know these techniques and keep your system protected against potential threats.
We hope this post would help you know How to Fix the 16 New LPE and ACE Vulnerabilities in HP BIOS. Thanks for reading this threat post. Please share this post and help to secure the digital world. Visit our social media page on Facebook, LinkedIn, Twitter, Telegram, Tumblr, Medium & Instagram, and subscribe to receive updates like this.
You may also like these articles:
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.