Table of Contents
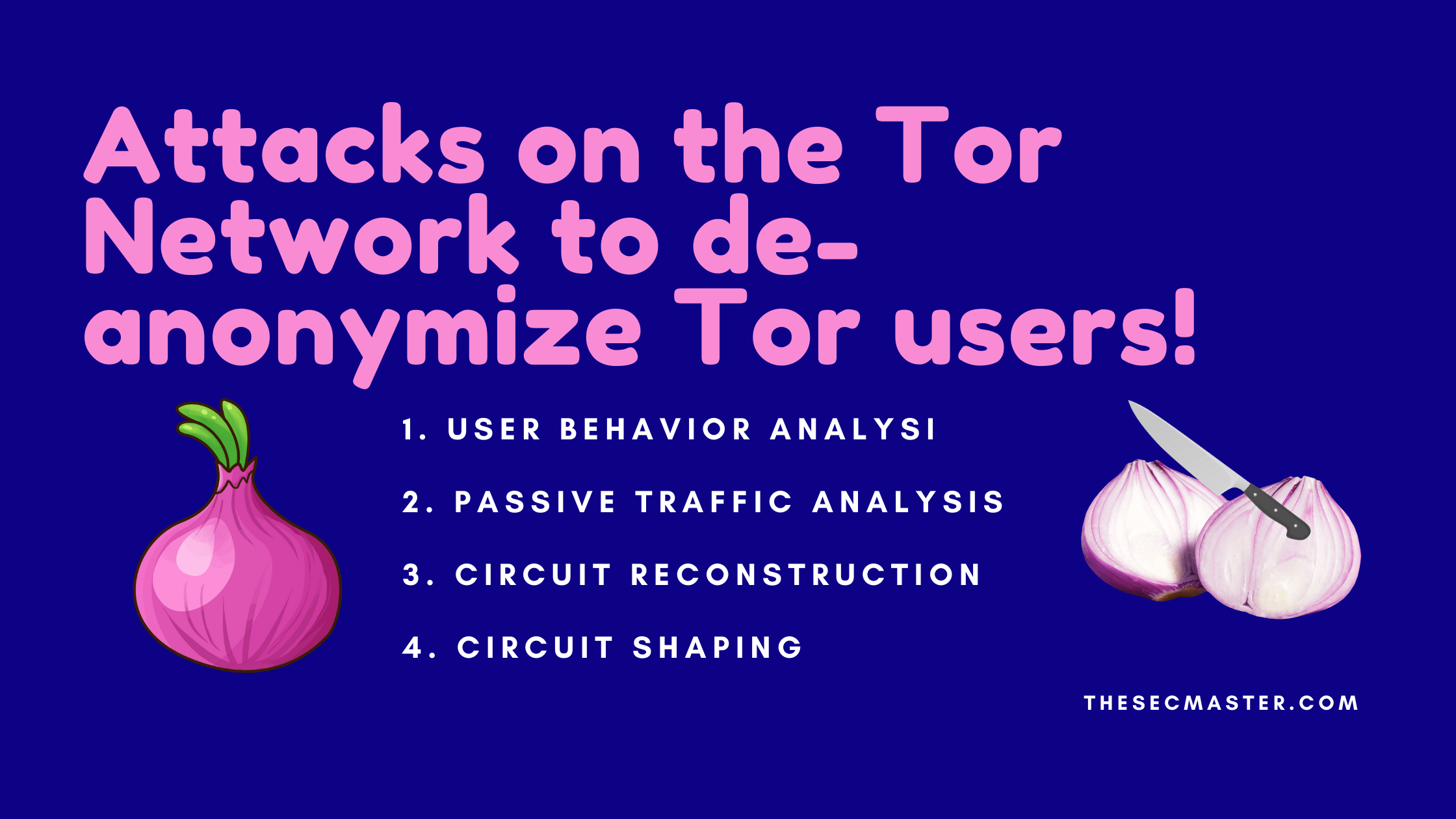
4 Types of Attacks on the Tor Network to De-Anonymize Tor Users:
Many of us may think Tor is the most secure network. Moreover, they also believed that using a VPN with Tor would make it impossible to break. But, the truth is something away from these thoughts. When it comes to attacks, Tor is no exception. There might be several attacks on the Tor. But, we have listed four such real-world attacks on Tor which are carried out by US National Security Agency (NSA) and UK General Communication Headquarters (GCHQ) to de-anonymize Tor users.
I would like to thank Edward Snowden, who created a presentation “
“, which includes a wide variety of exploitation and attacks on the Tor communication networks. This article covers five such attacks on the Tor network. And how governments and security agencies try to de-anonymize Tor users.
Before we jump to learn the attacks on Tor, we recommend reading the “Detailed anatomy of the Tor network” post, which gives details about the structure of the Tor network because it is required to know the Tor network to understand the attacks on the Tor.
Thanks to Lawrence Systems for creating this video.
1. User Behavior Analysis:
This attack targets the traffic between Tor’s Exit node and the destination site. The exit node is the node that communicates to the destination site on the internet. This is the point where all the Tor traffic will come out of the Tor network to join with other internet traffic. This gives a great opportunity for government agencies to de-anonymize Tor users. This technique just works by monitoring and analyzing the traffic of anonymized users leaving Tor exit nodes and correlating the traffic with available information.
Government agencies generally look for this information to de-anonymize Tor users:
Plane HTTP traffic between the exit node and the destination site.
Users were logging in to their personal accounts over Tor which revealed their identity.
Observe the activities of the users by mapping the anonymous Tor traffic and regular internet.
Compare the characteristics of anonymized and non anonymized users.
Agencies try to de anonymize the users using browser cookies. Cookies on the Tor and internet traffic may reveal the user identity and behaviour.
Countermeasures:
The tips that we have given in the article “6 simple tips to remain anonymous on the dark web!” will protect you from these attacks.
2. Passive Traffic Analysis:
Passive Traffic analysis is quite similar to User Behavior analysis. Both analysis techniques will try to tie the Tor and regular internet traffic to de-anonymize Tor users. Then, you may ask what makes Passive Traffic analysis different from the User Behavior analysis attack. User Behavior analysis depends on the insecure activities of the users, where Passive Traffic analysis looks for the patterns of a computer, browser, and network.
For example, A user will have a unique combination of entities. Like Operating System version, Installed patches, Browser version, Screen resolution, System time zone, A Plenty of system hardware and software properties. If those combinations appear in both Tor and regular internet traffic, it could be possible to tie the two traffic together to de-anonymize the users. In the billions of users on the internet, it is hard to tie the users as most of the users use common hardware and software. So, figuring out the perfect signature for a user is a tedious task.
Another smart way to do Passive Traffic analysis is to monitor the Tor’s entry node and exit node to figure out what happened inside the Tor network.
Countermeasures:
There is nothing much users can do to protect themselves from these attacks. Users have to ensure all the software they use is up to date. Especially the Tor browser.
3. Circuit Reconstruction:
It’s not a secret that the Tor network creates a virtual circuit by selecting random nodes. The idea behind this attack is to reconstruct the circuit between entry and exit nodes. If it had been possible to reconstruct the circuit, it would not have remained private and anonymous. This attack is directly targeting the perfect forward secrecy, which is the core tech behind the Tor network. Please read the “What does happen inside the Tor network?” post to understand how the Tor network operates.
In the Tor network, all the nodes operate in anonymous mode. Nobody knew the identity of the Tor node. Mover over, any individual or company can create a Tor node and joins the Tor network to accept traffic. There is not much control over the Tor nodes. Tor browser selects a random node to construct the circuit. Nobody has an idea about the selection of the Tor node and circuit path. On top of that, all the nodes operate in perfect forward secrecy mode, which enables the Tor nodes to hide the real identity of the source and destination. A Tor node can only know the identity of its direct peers.
Let’s understand this attack theoretically and calculate the success rate of the attack. If you want to compromise the Tor network, then you need to set up a malicious Tor node and join your node to start accepting the Tor traffic. But, the problem is you never come to know the real identity of the source and destination because of perfect forward secrecy. You may need to own all the nodes to reconstruct the circuit, which is impractical. But what if a wealthy advisor creates large numbers of nodes and adds them to the network over time? Tor network has roughly 9000 nodes running in 2021. If the Advisory creates 3000 nodes and adds them to the Tor network, then it becomes a matter of probability. In this scenario, the Advisory owns approximately 30% of the nodes. Then there may be a chance where the Advisory can control 30% of the Tor traffic. If a user selects a three-node circuit, there might be a chance of 30 % of the node would be controlled by the Advisory. In this way, when it is calculated for each combination of three-node circuits, The Advisory’s chances of controlling the Tor traffic is 2.7%, which is not worth it. This clarifies Circuit Reconstruction attack is practically not possible at this time.
| Number of nodes in a circuit | Compromise probability |
| 3 | 2.7% |
| 4 | 0.8% |
| 5 | 0.2% |
| 7 | 0.02% |
| 10 | 0.0006% |
Countermeasures:
As an individual user, you can’t stop a wealthy Advisory. What you can do as an individual user is, use simple logic. As more nodes as you have in your circuit, there is a lower probability of getting compromised. Increasing the size of the circuit definitely increase the security but reduces the performance.
4. Circuit Shaping:
A successful Circuit Reconstruction attack needs a large number of compromised or owned nodes. What if an attacker can control the Victim’s circuit with a small number of compromised nodes? In the Circuit Shaping attack, the attacker compromises the Victim’s computer or Tor browser and modifies the Tor browser to only use the compromised nodes instead of random nodes. Circuit Shaping attack needs two things primarily. Either attacker should have access to the Victim’s computer and alter the Tor. Or, the attacker forces the user to download and install the modified version of Tor.
Countermeasures:
Follow Security best practices & Use antimalware applications: Users need to follow all the security guidelines and install the best antivirus system to protect from this attack.
Download the Tor browser official site: Make sure you, as a user, only download the Tor from its official website.
Verify the Tor Browser’s signature: Always ensure the Tor browser you downloaded has not been tampered with. Please check out how to verify the Tor Browser’s signature from its official documentation.
Is It Possible To De-Anonymize a Tor User?
To conclude the answer to this question. De-anonymizing Tor users aren’t just theoretical. The governments have caught many Tor users and detained them for illegal activities. One such example is silk road an online dark website hosted in 2011 by Ross Ulbricht to trade illegal drugs. According to Edward Snowden, it is never possible to de-anonymize all Tor users at once. But, with manual analysis, it is possible to de-anonymize a very small fraction of Tor users. Till now, no success has been seen in de-anonymizing a user based on the request or demand.
Conclusion:
Tor is safe to use until all the security measures are taken. It is easy to de-anatomize a user if the user fails to follow the security measures. Tor is safe to use until all the security measures are taken. It is easy to de-anatomize a user if the user fails to follow the security measures.
Thanks for reading this article. Please visit thesecmaster.com and leave your comments.
You may also like these articles:
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.