Table of Contents
How To Fix The New OMI Vulnerabilities Target Linux VMs On Azure Environment?
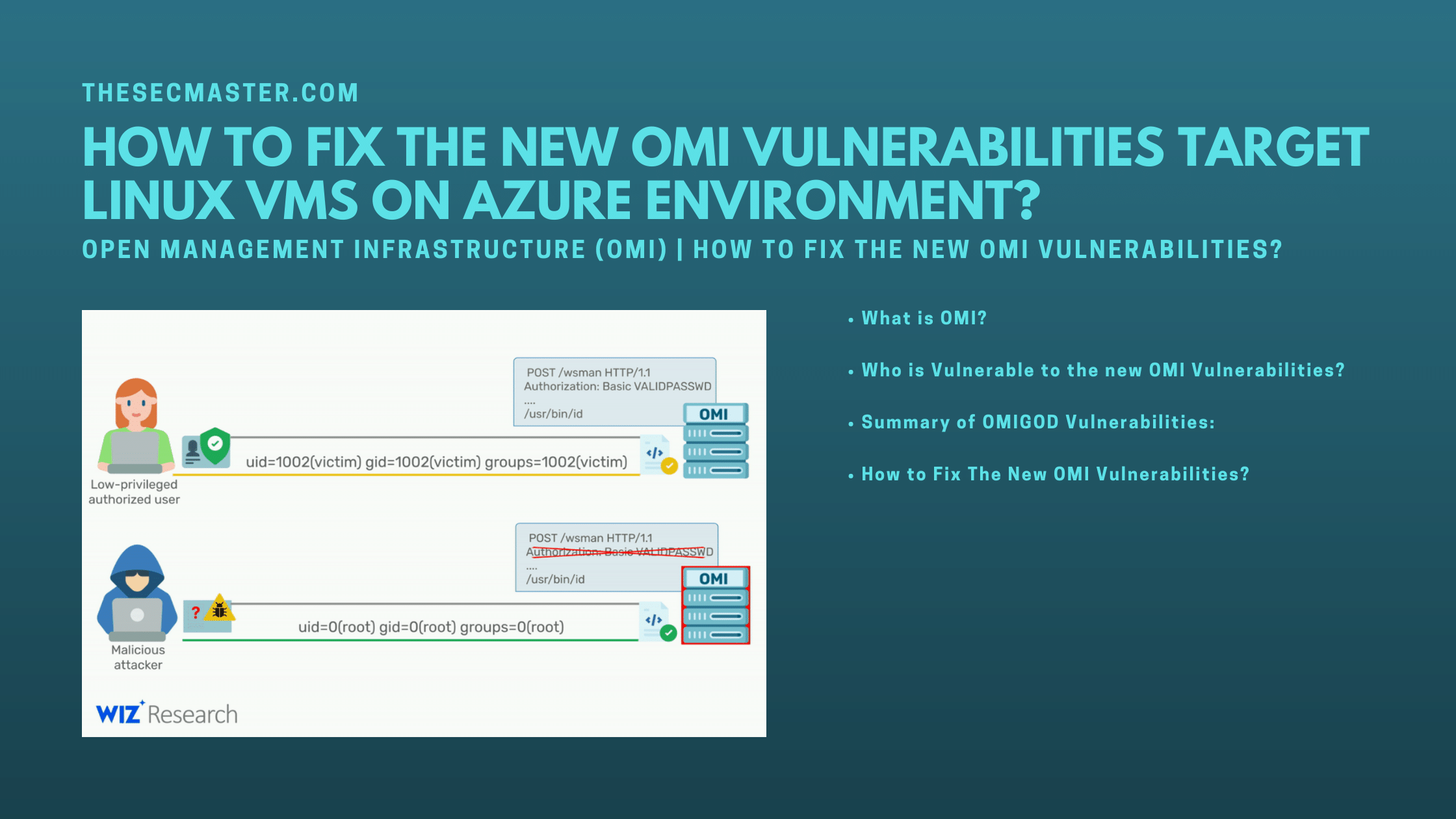
After CVE-2021-40444 – MSHTML Remote Code Execution Vulnerability. On September 14, Microsoft has confirmed four new vulnerabilities on Open Management Interface (OMI) that Microsoft installed on its Azure Linux VMs. It is estimated that thousands of Azure customers and millions of endpoints are affected by these vulnerabilities. Let’s see how to fix the new OMI vulnerabilities that target Linux VMs on its Azure platform.
What Is OMI?
Open Management Infrastructure (OMI) is an open-source project which comes as a pre-installed application on Azure Linux VMs. Microsoft secretly installs this on its Linux VMs to enable monitoring, logging, reporting, and host management options from the cloud provider’s user interface and APIs. OMI is the Linux/Unix equivalent of Windows Management Instrumentation and Remote Management (WMI/WinRM) which is used to manage desired-state configuration on Linux operating systems such as CentOS, Debian, Oracle Linux, Red Hat Enterprise Linux Server, SUSE Linux, and Ubuntu.
Who Is Vulnerable To The New OMI Vulnerabilities?
According to the report, when Azure customers enable any of these services: Azure Automatic Update, Azure Automation, Azure Operations Management Suite (OMS), Azure Configuration Management, Azure Log Analytics, and Azure Diagnostics services on Linux VMs, OMI is silently installed on them without the customer’s knowledge. Wiz security researcher Nir Ohfeld also said that these new OMI vulnerabilities are not just limited to cloud customers. It affects Linux machines deployed on on-premise on which OMI has been installed.According to Microsoft, any customers who enable these below services on their Linux VM instance are vulnerable to the OMIGOD vulnerabilities. It is estimated that thousands of Azure customers and millions of endpoints are affected by these vulnerabilities.
Azure Automation
Azure Automatic Update
Azure Operations Management Suite (OMS)
Azure Log Analytics
Azure Configuration Management
Azure Diagnostics
Azure Container Insights (Added September 16, 07:00AM EST)
Summary Of OMIGOD Vulnerabilities:
From Wiz Research Team
These are the four vulnerabilities collectively named OMIGOD vulnerabilities.
CVE-2021-38647 – Unauthenticated RCE as root (Severity: 9.8)
CVE-2021-38648 – Privilege Escalation vulnerability (Severity: 7.8)
CVE-2021-38645 – Privilege Escalation vulnerability (Severity: 7.8)
CVE-2021-38649 – Privilege Escalation vulnerability (Severity: 7.0)
The first remote code execution vulnerability CVE-2021-38647 lets adversaries gain remote access to Linux machines when OMI exposes the HTTPS management port publicly via TCP ports 1270, 5985, and 5986. later the adversaries carry out privilege escalation attacks on them and further compromise more VMs through the compromised VMs. These vulnerabilities allow attackers to remotely execute codes as a root user to exfiltrate sensitive data from the Linux VMs.
From Wiz Research Team
How To Fix The New OMI Vulnerabilities?
There are few mitigations and fixes available to protect from the new OMI vulnerabilities to answer this question. Let’s list them one after another.
Microsoft has released a fix for these new OMI vulnerabilities as part of its Patch Tuesday updates.
Install the MSRepo on your Linux VM. Please visit this page to learn how to install MSRepo.
Upgrade or install the latest OMI (version equivalent or greater than 1.6.8.1). Use these commands to upgrade or install the OMI on Debian and RedHat-based distributions.
Run this on Debian distro: $ sudo apt-get install omi
Run this on RedHat based distro: $ sudo yum install omi
Don’t deploy OMI from the System Center because the Linux agents could be decrypted. So we recommend using a manual way to upgrade or install OMI agents.
Uninstall OMI if not required.
Run this on Debian distro: $ sudo apt remove omi
Run this on RedHat based distro: $ sudo yum remove omi
You can identify your system is vulnerable just by checking the OMI ports enabled on your Linux instances. Block the post either on public-facing firewalls or internal firewalls as per your need.
Run this command to see the ports opened on your Linux: $ sudo netstat -antp | grep <post number>
Thanks for reading this threat post. Please share this post and help to secure the digital world. Please visit our social media page on Facebook, LinkedIn, Twitter, Telegram, Tumblr, & Medium and subscribe to receive updates like this.
You may also like these articles:
How To Protect Azure Active Directory From Undetected Brute-Force Attacks?
How To Fix CVE-2022-0492- Privilege Escalation And Container Escape Vulnerabilities In Cgroups
How To Fix The Dirty Pipe Vulnerability In Linux Kernel- CVE-2022-0847
How Attackers Abused Kubeflow To Run Crypto Mining Campaigns Targeting Kubernetes Clusters
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.