Table of Contents
New Apple’s 0-Day Vulnerability – Update Your Apple Products Immediately
On Monday, Apple rolled out a patch for new Apple’s 0-day vulnerability. We ask all our readers to update their iPhone to iOS 14.7.1, iPad to iPadOS 14.7.1, and macOS to Big Sur 11.5.1.
Apple said that it had released 13 security updates with the release of this update. According to the company, this memory corruption vulnerability (CVE-2021-30807) in the IOMobileFrameBuffer component may have been actively exploited in the wild. Apple didn’t disclose more details on the 0-day vulnerability for security reasons. You can visit the Apple security updates page to see the recently released updates.
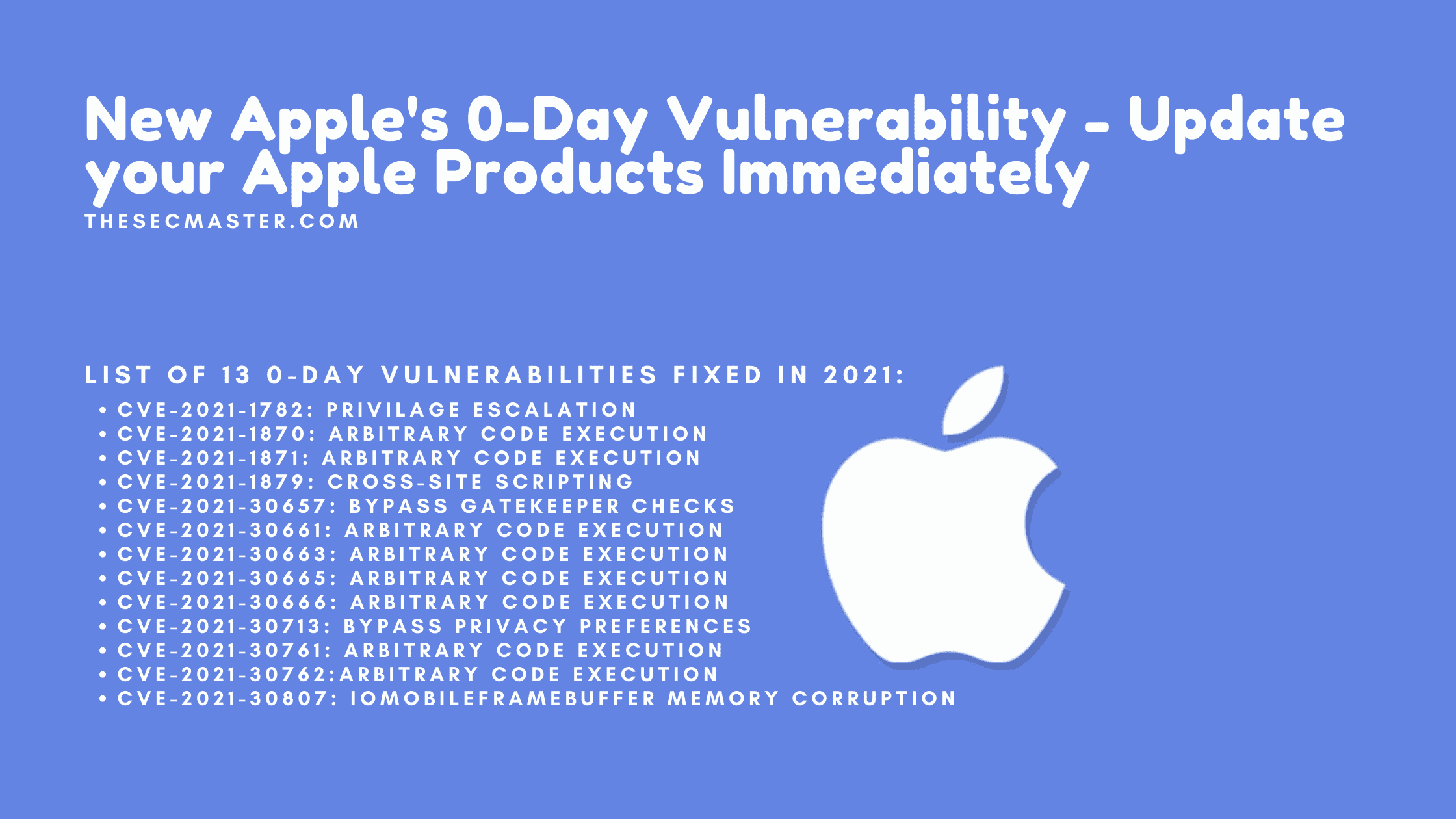
List of 13 0-day vulnerabilities Fixed in 2021:
CVE-2021-1782: Privilage Escalation
CVE-2021-1870: Arbitrary Code Execution
CVE-2021-1871: Arbitrary Code Execution
CVE-2021-1879: Cross-Site Scripting
CVE-2021-30657: Bypass Gatekeeper checks
CVE-2021-30661: Arbitrary Code Execution
CVE-2021-30663: Arbitrary Code Execution
CVE-2021-30665: Arbitrary Code Execution
CVE-2021-30666: Arbitrary Code Execution
CVE-2021-30713: Bypass Privacy Preferences
CVE-2021-30761: Arbitrary Code Execution
CVE-2021-30762:Arbitrary Code Execution
CVE-2021-30807: IOMobileFrameBuffer Memory Corruption
Apple’s Recommendation:
Apple urged to install the security updates as soon as possible on iPhone, iPad, and mac to be secure themselves from the attacks that targetted Apple’s 0-Day vulnerability.
You may also like these articles:
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.